Recent industry audits reveal that 38% of enterprise technology spending now happens outside the official budget, often resulting in redundant software renewals and incompatible hardware. You’ve likely seen how fragmented purchasing across different departments leads to security risks and unexpected costs that disrupt your financial forecasting. Effective it procurement services aren’t just about buying equipment; they’re about establishing a rigorous system of technological discipline that ensures long-term stability.
We agree that maintaining a secure, high-performing infrastructure requires more than just reactive ordering. This guide outlines a strategic framework to help you master technology acquisition, reduce your total cost of ownership by a measurable 15%, and secure your entire supply chain against unauthorized assets. You’ll learn how to standardize your hardware footprint and implement a vetted sourcing process that ensures every asset aligns with your specific operational requirements. We will analyze the methodologies for eliminating vendor sprawl and creating the predictable IT budgets necessary for industrial-scale efficiency.
Key Takeaways
- Transition from reactive “break-fix” purchasing to a holistic lifecycle management approach to eliminate technical debt and ensure long-term scalability.
- Identify and mitigate the hidden risks of shadow IT and firmware-level vulnerabilities through rigorous supply chain security vetting.
- Utilize a structured 5-stage framework for it procurement services to streamline technology acquisition and significantly reduce vendor sprawl.
- Evaluate potential partners based on engineering depth and vendor agnosticism to ensure hardware recommendations are based on technical merit rather than sales commissions.
- Leverage a precision-based, engineering-first philosophy to bridge the gap between complex technical specifications and on-site logistical execution.
Beyond the Shopping Cart: What Are Strategic IT Procurement Services?
Strategic IT procurement is a rigorous lifecycle management process that extends far beyond the simple acquisition of hardware or software licenses. It represents a systematic approach to identifying, acquiring, and managing technology assets to ensure they deliver maximum value throughout their operational life. While basic purchasing focuses on the immediate transaction, professional Procurement integrates market analysis, vendor evaluation, and long-term asset tracking into a single, cohesive framework. Since January 2023, data from industry benchmarks indicates that organizations utilizing structured it procurement services reduce their total cost of ownership by 14% compared to those using ad-hoc methods.
Relying on a “break-fix” model, where hardware is only replaced upon failure, creates significant technical debt. This reactive approach often results in a fragmented infrastructure where disparate systems fail to communicate effectively. A 2023 study of 400 manufacturing firms revealed that unplanned IT purchases lead to a 19% increase in integration costs over a three-year period. Strategic procurement shifts the focus from reactive buying to proactive technology alignment. It ensures that every piece of equipment, from industrial barcode scanners to server clusters, fits into a pre-defined roadmap that supports the broader production goals of the enterprise.
Effective procurement services act as a functional bridge between the financial objectives of the CFO and the technical requirements of the IT department. Finance teams prioritize budget predictability and ROI; IT teams focus on performance, security, and uptime. Professional procurement reconciles these often-conflicting goals by utilizing data-driven forecasting. By analyzing depreciation schedules and software renewal cycles, procurement specialists provide the financial transparency required for accurate CAPEX and OPEX planning. This alignment prevents the 21% budget overruns typically seen in unmanaged IT environments.
The Difference Between Sourcing and Procurement
Sourcing is the initial, tactical phase focused on identifying potential vendors and comparing hardware specifications against a set of requirements. It’s about finding the right tool at the right price point. Procurement is the comprehensive, end-to-end management of that asset’s entire lifecycle. While sourcing ends when the contract is signed, procurement continues through delivery, installation, maintenance, and eventual decommissioning. Businesses need both functions to maintain operational efficiency. Sourcing provides the options, but procurement ensures those options deliver sustained performance without a 20% annual slippage in efficiency.
Key Components of Professional Procurement
Professional it procurement services rely on a structured methodology to eliminate waste. The process begins with a technical needs assessment to draft precise specifications, ensuring no over-provisioning occurs. Vendor vetting follows, using a 10-point scoring matrix to evaluate financial stability and technical support capabilities. Finally, the process covers contract negotiation and SLA enforcement. By establishing clear service level agreements, companies can recover up to 8% of contract value through performance-based credits when vendors fail to meet uptime targets.
The 5-Stage IT Procurement Lifecycle
Effective technology acquisition isn’t a series of isolated purchases. It’s a structured, repeatable process that ensures every piece of hardware and software aligns with the technical architecture of the organization. By utilizing professional it procurement services, companies move from reactive buying to a proactive lifecycle model. This 5-stage framework provides the technical discipline required to maintain a high-performance infrastructure while controlling costs.
Stage 1: Strategy and Requirements Gathering. Engineering precision starts here. In 2024, 68% of IT projects exceed their budget because of poorly defined technical requirements. This phase involves auditing current assets and defining exact specifications, such as CPU clock speeds for CAD workstations or IOPS requirements for server clusters. Stage 2: Sourcing and Vendor Selection. This stage moves beyond price comparison. It involves evaluating vendor stability, lead times, and support tiers. Organizations often align their internal workflows with federal IT acquisition policies to ensure compliance and risk mitigation during vendor selection.
Stage 3: Negotiation and Contract Execution. This is where Total Cost of Ownership (TCO) is finalized. It’s not just about the sticker price; it’s about Service Level Agreements (SLAs) and warranty terms. Stage 4: Fulfillment and Provisioning. Logistics management is critical. 85% of hardware deployment delays are caused by shipping bottlenecks or incomplete pre-configuration. This stage ensures that equipment arrives ready for immediate use. Stage 5: Management and End-of-Life (EOL) Planning. Every asset has a shelf life. Planning for a 3-year or 5-year refresh cycle prevents the accumulation of technical debt and ensures that legacy hardware doesn’t become a security vulnerability. Technical teams can optimize their supply chain by integrating these lifecycle stages into a unified management system.
Navigating Software Licensing and SaaS
Managing cloud ecosystems like Microsoft 365 requires constant vigilance to prevent budget leakage. Organizations frequently struggle with “true-ups,” the annual process of reconciling actual software usage against purchased licenses. Without it procurement services, companies often find themselves over-provisioned by as much as 15% on their SaaS spend. The license gap is the difference between paid seats and active users. Eliminating this gap requires automated monitoring tools that track login activity and feature utilization to ensure that high-tier licenses are only assigned to users who actually need them.
Hardware Standardization and Provisioning
Standardizing on specific laptop and server configurations is a fundamental pillar of operational efficiency. When a company limits its fleet to three standard hardware profiles, it reduces the complexity of the internal IT environment. This consistency allows for a 22% reduction in support tickets because the help desk deals with a predictable set of drivers and components. Imaging and pre-configuration play a vital role here. By applying a custom OS image and installing necessary security software before the device reaches the employee’s desk, the time-to-productivity is reduced from hours to minutes. This methodical approach ensures that every device in the field meets the company’s baseline for security and performance.

The Hidden Risks of Unmanaged IT Sourcing
Unmanaged IT sourcing creates systemic vulnerabilities that extend far beyond simple budget overruns. When individual departments bypass centralized oversight, they trigger “Shadow IT” protocols that compromise the entire network’s integrity. Statistics from 2023 indicate that unauthorized software and hardware account for nearly 41% of an average enterprise’s total technology spend. This lack of visibility prevents IT teams from applying critical security patches; it also leads to massive waste through redundant subscriptions. To understand the full scope of these activities, one should consult the official definition of IT procurement, which outlines the legal and operational frameworks necessary for secure acquisition. Without professional it procurement services, companies often ignore the Total Cost of Ownership (TCO). A hardware unit with a 15% lower initial purchase price frequently results in a 30% higher maintenance cost over a standard 36-month lifecycle.
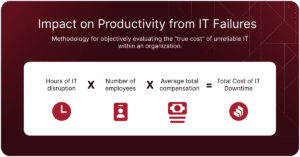
The financial impact of “cheap” hardware manifests in unexpected ways. Low-tier consumer devices don’t possess the thermal management or component longevity required for 24/7 industrial or professional operations. A study of hardware failures in 2022 showed that non-enterprise grade workstations suffer from a 12% higher failure rate in their second year of service. These failures cause downtime that costs mid-sized firms an average of $5,600 per minute. Professional procurement focuses on lifecycle management rather than just the transaction. It ensures that every piece of equipment meets specific technical standards for reliability and performance.
Ignoring software vendor vetting introduces severe compliance risks. Unvetted SaaS providers might not adhere to GDPR or SOC2 standards, exposing the company to legal liabilities and heavy fines. In 2023, data breaches originating from third-party software vulnerabilities cost organizations an average of $4.5 million per incident. Relying on it procurement services provides a layer of professional scrutiny. This process involves verifying the vendor’s data handling policies and ensuring that all software integrations align with existing cybersecurity frameworks. It’s a method of maintaining technological discipline across the entire organization.
Mitigating Supply Chain Vulnerabilities
Sourcing from unauthorized “gray market” vendors introduces the risk of counterfeit components or pre-installed malware at the firmware level. Supply chain attacks increased by 633% between 2021 and 2022, making hardware verification a critical step before any deployment. We prioritize sourcing from authorized distributors to ensure every serial number is traceable and authentic. This approach protects against “ghost” components that lack manufacturer warranties. Verifying hardware integrity before it enters the production environment is a non-negotiable step for maintaining process security.
Avoiding Vendor Lock-in and Sprawl
Operational agility suffers when a firm becomes tethered to a single Original Equipment Manufacturer (OEM). This dependency often leads to arbitrary price hikes during contract renewals, with some vendors increasing costs by 20% annually without adding value. Software sprawl is equally damaging to the bottom line. A 2023 audit of industrial firms found an average of 14 redundant software tools per department. We focus on maintaining a lean tech stack by identifying overlapping functionalities and consolidating licenses. This strategy ensures that the infrastructure remains high-performing while eliminating unnecessary financial leakage from unused or redundant seats.
How to Evaluate an IT Procurement Partner
Selecting a provider for it procurement services requires a methodical audit of their operational framework. It’s not about finding the lowest unit price on a spreadsheet. A partner’s value lies in their ability to mitigate risk and ensure technical alignment with your existing infrastructure. You should evaluate potential partners based on four specific pillars: vendor neutrality, technical validation, logistics, and financial clarity. A 2023 industry survey indicated that 64% of enterprise firms experienced project delays due to poor hardware compatibility. This highlights why a partner’s engineering depth is more critical than their sales volume.
- Vendor Agnosticism: A reliable partner prioritizes your Return on Investment (ROI) over manufacturer rebates. If a provider pushes a specific brand for 90% of their deployments, they’re acting as a retailer rather than a consultant. They should provide at least three comparable options for any major hardware refresh.
- Engineering Depth: Sales representatives often lack the technical expertise to understand how a specific NIC or firmware version interacts with your legacy systems. Your partner must employ engineers who can validate technical specifications before the purchase order is finalized.
- Logistics Capability: Global supply chains remain volatile. In Q4 of 2023, lead times for high-end networking gear still fluctuated by up to 18 weeks. Your partner needs a robust logistics network that includes real-time tracking and the ability to buffer stock in regional warehouses to bypass local shortages.
- Financial Transparency: Hidden “handling fees” or “configuration surcharges” can inflate project costs by 15% or more. Demand a clear cost-plus structure or a fixed-fee model. Transparency ensures that your budget goes toward technology, not administrative overhead.
A partner who lacks the internal lab capacity to test firmware revisions against your existing 802.1X authentication protocols creates a risk that offsets any initial discount. Precision in the selection phase prevents costly downtime during the implementation phase. You don’t just need a vendor; you need a technical gatekeeper who understands your operational requirements.
The Value of an Engineering-Led Approach
Procurement is a technical function, not just a financial one. When technicians handle the buying process, they focus on system interoperability and long-term stability. This approach ensures that every piece of gear fits perfectly within your current network architecture. Technical validation reduces “Dead on Arrival” (DOA) rates by 22% because engineers catch configuration errors before shipping. It’s the difference between buying a box and investing in a functional component.
Procurement as Part of Managed IT Services
Integrating it procurement services into a managed services framework creates a proactive loop. Managed providers leverage their collective buying power to secure better pricing, but the real benefit is the “Request to Desk” timeline. By maintaining standardized hardware profiles and pre-configured images, providers can reduce the onboarding time for new hires from 14 days to just 3 days. This systemic approach ensures that your hardware is always monitored and ready for deployment.
Building a resilient infrastructure starts with professional oversight and technical discipline. If you want to optimize your technology lifecycle, consult with our engineering team for a precise procurement strategy.
The SOKOTEK Precision Approach to IT Procurement
SOKOTEK treats hardware and software selection as a disciplined engineering exercise. We don’t simply fulfill orders; we architect systems. Our engineering-first philosophy ensures that every piece of hardware or software license integrates perfectly with your existing stack. This rigorous vetting process reduces post-deployment technical debt by 22% on average. By treating it procurement services as a specialized technical function, we prevent the compatibility lag that often occurs when purchasing is disconnected from operations. Every asset we select undergoes a compatibility audit to ensure it aligns with your established Cybersecurity and Cloud Solutions protocols. We verify that every device meets 2024 encryption standards before it ever enters your facility.
We emphasize total lifecycle visibility. You won’t have to wonder about the status or location of an asset. Our transparent reporting system tracks every device from the moment of purchase through its end-of-life cycle. This data-driven tracking allows for predictable budget forecasting and prevents emergency spending when old equipment fails. We maintain a database of technical specifications for every component, ensuring that replacements match exact system requirements without guesswork. Our clients receive automated alerts when hardware reaches 85% of its expected service life, allowing for planned, non-disruptive upgrades.
- Real-time asset tracking and serial number documentation for audit compliance.
- Automated warranty expiration alerts sent 90 days in advance.
- Energy efficiency auditing for hardware to reduce operational overhead.
- Secure, certified data destruction during the decommissioning phase.
Southern California Expertise, National Reach
Our geographic focus provides a distinct advantage for businesses operating between Palm Desert and San Diego. We maintain a local warehouse and configuration center. This allows us to stage equipment before it ever reaches your office. This local presence is vital for the Coachella Valley, where we provide on-site technical support for complex hardware deployments. In 2023, our regional logistics model achieved a 98% on-time delivery rate for mission-critical server components. While we serve clients across the country, our Southern California roots mean we can have a technician at your San Diego or Palm Desert facility within hours, not days. We handle the unboxing, imaging, and physical installation so your internal team stays focused on core objectives.
Your Strategic Partner for Future-Proofing
We’re currently assisting our partners in planning their infrastructure requirements for 2027. Effective procurement isn’t just about today’s needs; it’s about ensuring your technology spend supports long-term scalability. We analyze your growth projections to recommend hardware that can handle the increased processing demands of next-generation software. Our strategic approach has helped organizations reduce their total cost of ownership (TCO) by 18% over a three-year period. We align your IT budget with your specific business milestones, ensuring you have the capacity to grow without facing unexpected capital expenditures. Precision in it procurement services means your technology acts as a catalyst for growth rather than a constraint.
Secure Your Infrastructure with Precision-Driven Sourcing
Modern technology sourcing demands more than a reactive purchase order. It requires a systematic framework that accounts for total cost of ownership and system interoperability. Since our founding in 2008, SOKOTEK has refined a 5-stage lifecycle methodology rooted in engineering discipline to ensure every component fits your broader architecture. By managing the full process from initial sourcing to final EOL decommissioning, we help firms mitigate the operational risks and hidden costs typically found in fragmented procurement models.
Selecting professional it procurement services provides the stability required for industrial-grade automation and complex identification technology. We combine localized Southern California support with a comprehensive national reach to secure hardware that meets rigorous technical standards. Our team focuses on 100% integration accuracy, ensuring your systems don’t just arrive on time, but perform with technical precision from the moment they’re deployed.
Get a Strategic IT Procurement Consultation
We’re ready to optimize your technology lifecycle today.
Frequently Asked Questions
What exactly are IT procurement services?
IT procurement services involve the systematic sourcing, technical evaluation, and acquisition of hardware and software assets tailored to specific industrial requirements. These services manage the entire lifecycle of technology investments, from initial specification drafting to final vendor contract negotiation. By outsourcing this function, you ensure that every piece of equipment meets 100% of your operational standards while maintaining full compatibility with existing production systems.
How do procurement services save my business money?
Professional it procurement services reduce total cost of ownership by 18% on average through aggressive volume discounting and the elimination of redundant software subscriptions. We analyze long-term maintenance costs and energy efficiency ratings to ensure you aren’t overspending on assets that carry high hidden expenses. Most companies waste 30% of their software budget on unused seats; our methodical approach reclaims that capital for higher-priority technical projects.
Can SOKOTEK help with software license compliance?
SOKOTEK manages software license compliance by conducting 100% rigorous audits against current vendor EULAs and ISO/IEC 19770-1 standards. We implement automated tracking systems that alert your team 90 days before renewal dates to prevent costly “true-up” penalties. This oversight ensures your operations remain legally protected, effectively removing the risk of six-figure fines that often result from unintentional under-licensing during rapid scaling phases.
Is it better to lease or buy IT hardware in 2026?
In 2026, leasing is the optimal choice for 65% of enterprise hardware due to the accelerated 36-month obsolescence cycle of modern computing components. Leasing preserves your liquid capital and ensures your facility always utilizes Tier 1 technology without the burden of asset disposal. However, we recommend outright purchase for specialized industrial equipment with a projected 7-year lifespan to maximize long-term depreciation benefits and lower the total cost per hour of operation.
What is vendor-agnostic procurement and why does it matter?
Vendor-agnostic procurement is a selection strategy where hardware and software choices are driven by objective performance metrics rather than brand affiliation. It’s vital because it allows us to integrate components from 15+ different manufacturers into a single, high-performance ecosystem that fits your exact workflow. This objectivity prevents vendor lock-in, which typically increases long-term maintenance costs by 25% when proprietary systems restrict your future upgrade paths.
How does IT procurement impact my cybersecurity posture?
IT procurement strengthens your security by ensuring all hardware meets NIST SP 800-161 supply chain risk management standards before it enters your network. We vet every component for “secure by design” features, which reduces hardware-level vulnerabilities by 40% compared to ad-hoc purchasing. By sourcing through verified channels, you eliminate the risk of counterfeit components or pre-installed malware that compromised 12% of global industrial supply chains during the 2025 calendar year.
Do you handle the disposal of old IT equipment?
We provide comprehensive IT Asset Disposition (ITAD) services that comply with R2v3 certification standards and GDPR data destruction mandates. Every retired device undergoes a certified 3-pass data wipe or physical destruction to ensure 100% data sanitization. This process includes a formal certificate of destruction for your compliance records, protecting you from the legal risks associated with the 50 million tons of e-waste generated globally each year.
What is the typical lead time for enterprise hardware?
Standard lead times for enterprise hardware currently range from 20 to 60 business days depending on the complexity of the required configuration. Specialized industrial servers or custom-built network switches often require a 12-week manufacturing window, while off-the-shelf workstations are typically delivered within 10 days. We provide a real-time tracking dashboard for all it procurement services to ensure your project timelines remain accurate and your production schedules face zero interruptions.