Why Cheap IT Providers Are Costing Businesses More in the Long Run
It starts with a seemingly harmless $500 savings on your monthly technology invoice. However, that thrifty choice often ends on a Tuesday morning with your entire staff sitting completely idle because a crucial system crashed, abruptly costing you $5,000 in lost productivity by noon. Many business leaders mistakenly treat their digital infrastructure as a standard utility, assuming the lowest bid is always a strategic win.
Industry data reveals a much harsher reality, showing that the average cost of downtime for typical businesses can easily exceed $100 per minute. Relying on cheap IT providers creates massive financial leakage, turning minor maintenance delays into company-wide gridlock. Technology is not a utility bill; it is the vital engine powering your daily operations, and if that engine stalls out, the whole car stops regardless of how much you saved on the oil change.
Halting this invisible drain requires adopting a proactive, value-protection mindset rather than settling for price-only decisions. Recognizing the severe hidden costs of budget IT support is essential for safeguarding your operations.
The Mathematical Reality of Downtime: Why One Hour Offline Wipes Out a Year of Savings
Most business leaders know that when a key system crashes, work grinds to a halt. What is rarely measured is the exact financial toll this silence takes on the bottom line. Calculating the true total cost of ownership for business technology requires looking past the monthly vendor invoice to see the severe business impact of unplanned downtime. Saving $500 a month on a budget IT contract vanishes the moment a server failure wastes an entire Tuesday morning.
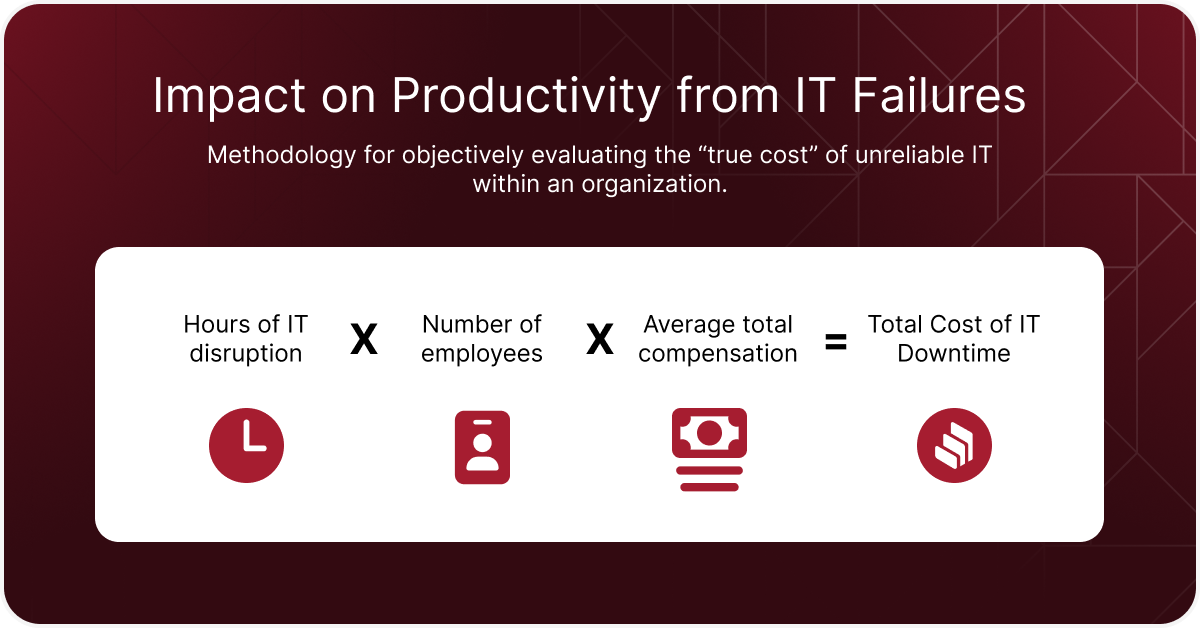
To understand the real stakes, you need to calculate your company’s “Downtime Hourly Rate.” This metric transforms abstract technical glitches into concrete financial data using this three-part formula:
- (Number of employees x hourly rate): The direct cost of paying your staff to sit idle.
- (Lost revenue per hour): The sales, billable hours, or production that completely stalled.
- (Brand recovery cost): The unrecoverable time spent apologizing to frustrated clients.
Once you see this total, the proactive network monitoring benefits become undeniable. Investing in a team that prevents outages yields a massive ROI compared to the bleeding hourly cost of halted operations. Yet, internal productivity loss is only one side of the cheap IT coin. Leaving systems unmonitored to save a few dollars turns a budget security strategy into an unlocked door for ransomware.
Why a Budget Security Strategy Is Just an Unlocked Door for Ransomware
Treating your network like a storage unit padlock is a dangerous game. Many leaders fall into the “set it and forget it” trap, assuming basic antivirus software is enough to keep their data safe. But a cheap lock only works until a criminal actively tests the door. Discount IT providers routinely skip proactive patching—the critical process of applying software updates to fix invisible system vulnerabilities before hackers can exploit them.
When you accept the lowest bid, you secretly trade away primary defenses. Budget vendors often ignore daily backup verifications, disregard the security risks of outdated technology infrastructure, and fail to meet modern compliance requirements for data protection. The ROI of cybersecurity investments becomes brutally obvious immediately following a breach. While proactive prevention requires a predictable, manageable monthly expense, ransomware recovery costs demand catastrophic cash payouts and cause weeks of halted operations.
Business leaders who survive a breach quickly realize that cheap IT was actually a high-risk loan. The immense financial toll of recovering locked data vastly outweighs the price of maintaining strong defenses year-round. Ignoring necessary updates creates compounding problems, and every skipped security protocol directly feeds into the interest rate of technical debt, ensuring you are paying for yesterday’s shortcuts today.
The Interest Rate of Technical Debt: Paying for Yesterday’s Shortcuts Today
Every time you delay replacing an aging computer or apply a temporary patch to a failing server, you take out a loan against your company’s future. This compounding problem is known as technical debt in small business operations. Like financial debt, these shortcuts feel like a budget victory today, but you eventually pay them back with steep interest through lost employee productivity and sudden downtime.
Recognizing this hidden tax is the first step to protecting your bottom line. While hunting for affordable IT services, leaders frequently ignore the daily toll of outdated infrastructure. You can easily spot the signs of high technical debt in an office:
- Frequent software crashes.
- Slow login times.
- ‘Spaghetti’ wiring in the server room.
Shifting your focus from the initial purchase price to the total lifecycle value of your equipment stops this financial leakage. Implementing a strategic IT roadmap for business growth allows you to schedule predictable technology refresh cycles, replacing hardware before it inevitably fails. Ignoring these proactive upgrades keeps your team trapped in constant emergencies, making a reactive approach the most expensive way to operate.
Managed Services vs. Break-Fix: Why Waiting for Things to Break Is the Most Expensive Way to Operate
Most leaders initially treat technology like office plumbing, calling for help only when a digital pipe bursts. Paying strictly when systems fail sounds like smart budgeting on paper to a cost-conscious business owner. However, this reactive strategy transforms routine maintenance into chaotic, expensive emergencies that completely freeze your operations and drain company morale.
The fundamental flaw in waiting for disasters lies in conflicting financial goals. When analyzing the managed services vs break fix model, you realize reactive vendors actually profit from your company’s misery, billing hourly while your employees sit idle. This traditional structure essentially rewards your outsourced support for applying slow, temporary bandages rather than investing in permanent cures.
Shifting to a proactive partnership changes this dynamic entirely through a predictable, flat monthly rate. Because a managed team loses money if your server crashes, their financial incentives suddenly align perfectly with your productivity goals. You immediately capture proactive network monitoring benefits, allowing technicians to quietly resolve tiny glitches in the background before they ever escalate into a full workday disruption.
Evaluating what to look for in a managed service provider means prioritizing partners who prevent fires rather than simply charging to fight them. This vital transition secures a stable monthly budget while eliminating the hidden tax of reactive downtime. Yet, simply keeping the lights on is only the baseline expectation; the true threat surfaces when low-cost vendors stifle your business scalability.
When Your IT Becomes a Ceiling: How Low-Cost Vendors Stifle Business Scalability
Hitting your revenue goals feels incredible until your technology refuses to keep up. The scalability limitations of low-cost IT vendors become painfully obvious when operations outgrow their bare-bones support. Instead of driving expansion, a budget provider quickly turns into an IT bottleneck, lacking the foresight to upgrade systems before they buckle under increased daily workloads.
Evaluating this hidden risk requires a simple test: could your current setup handle doubling your staff tomorrow without performance collapsing? By measuring IT support value beyond price, you recognize that delayed onboarding, crashing software, and frustrated employees are the true costs of a reactive vendor. Genuine scalability demands a partner who anticipates operational friction before your team actually feels it.
Protecting your momentum means demanding a strategic IT roadmap for business growth during every quarterly review. This vital document shifts focus from fixing broken laptops to projecting future capacity needs. Failing to plan ahead does more than just stall expansion; it introduces severe vulnerabilities that can void your cybersecurity insurance.
The Compliance Gap: Why Cheap IT Can Void Your Cybersecurity Insurance
Buying a policy doesn’t guarantee a payout when a breach occurs. Meeting strict cybersecurity insurance eligibility requirements demands continuous management that budget vendors rarely deliver. During an incident, insurers actively scrutinize the security risks of outdated technology infrastructure. If they discover you ignored basic compliance requirements for data protection, they can deny your claim under a “negligence” clause, leaving your business to absorb the financial blow alone.
Protecting your coverage requires “Proof of Maintenance”—documented evidence that your provider actively defends your network. Unfortunately, cheap IT often misses these three common insurance requirements:
- Multi-Factor Authentication (MFA)
- Regular encrypted backups
- Documented patch logs
Securing these records avoids the negligence trap and ensures eligibility for lower premiums. Demanding this accountability ensures your operations remain protected, measurable, and resilient.
Beyond the Lowest Bid: 3 Metrics to Measure the True ROI of Your IT Support
Assessing what to look for in a managed service provider means focusing on business outcomes, not hourly rates. A low monthly fee is worthless if your team sits idle during an outage. Service Level Agreements (SLAs)—the written guarantees a vendor makes about their performance—are your safety net. Evaluating IT service level agreements translates technical promises into guaranteed employee productivity.
Instead of counting closed support tickets, start measuring IT support value beyond price by tracking total system uptime. You can separate proactive partners from reactive vendors by using this ‘Value Vetting’ checklist during interviews:
- Average Response vs Resolution Time: A quick “response” simply means they answered the phone; “resolution” dictates when your staff actually gets back to work.
- Percentage of Issues Fixed Proactively: Strong providers resolve background glitches before your team ever notices a slowdown.
- Annual Strategic Planning Hours: Dedicated time spent aligning technology upgrades with your future business goals.
Securing a partner committed to these metrics stops financial leakage and protects your daily operations. Proper accountability establishes a clear path to transition from cost-center IT to growth-engine technology.
Your 90-Day Roadmap to Transitioning from Cost-Center IT to Growth-Engine Technology
Settling for the lowest bid creates the highest risk for your operations. Instead of merely minimizing expenses, you can confidently protect your revenue by maximizing uptime. Start a 90-day action plan today by auditing recent downtime to uncover hidden productivity losses. Next, review the critical gaps your current budget model ignores. Finally, use these insights to seek a strategic partnership focused on proactive maintenance rather than cheap, reactive fixes.
Acknowledging the hidden costs of cheap IT fundamentally changes how you protect your team. As you evaluate truly cost-effective IT solutions, remember that premium support drives growth. By measuring the actual ROI of cybersecurity investments, you secure your company’s digital future. You are no longer just paying to keep the lights on; you are building a resilient, secure business.